What is “The Internet of Things”? Using Radio frequency Identification (RFID), electromagnetic pulses connect devices together by transmitting and communicating data. In other words, when devices connect to one another through cloud computing as a network (Internet, Bluetooth, etc).
While some may think it’s just a ‘passing fad’, we cannot deny that the IoT is becoming more prevalent in daily life.
Your iPhone is automatically storing your data on iCloud, connecting it automatically to your MacBook. Your contactless payment bank cards are constantly sending and transmitting data from a single tap. The IoT is designed to facilitate everyday life and make things happen in a much cooler, and of course, advanced way.
Whether it was your Siemens refrigerator reminding you that you are out of milk, your washing machine that can be controlled by your smartphone or your toaster that knows when to heat your bread so that it’s ready when you’re home, the IoT is doing some fascinating work. Even plants can be connected to the Internet today!

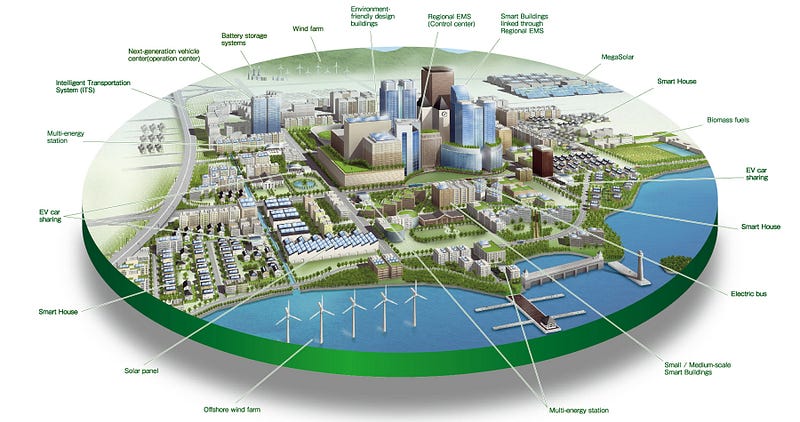
Here’s the ultimate goal, however: living in not just a smart home, but a ‘Smart City’.
The ideal, utopian world where a city is constantly connected — the development of a city that operates on a cloud network infrastructure full of connectivity. Eventually, this can even lead to a ‘Smart Nation’, where cities are connected to one another.
While this does seem to be such a utopian and surreal world, we must not overlook one of the most important things: our security. MIT Professor Sanjay Sarma shares his thoughts by saying:
“I helped invent the Internet of Things. Here’s why I’m worried about how secure it is”.
What happens if someone has access to all your connected devices? Here’s a video depicting what crime in the future of IOT could look like:
There are so many different concepts are expressed in that video: from drones and facial recognition to the connection of home devices and mobile devices. If all our devices are connected and our personal information is stored, just to what extent could we become vulnerable and susceptible to cyber crime?
Article by channel:
Everything you need to know about Digital Transformation
The best articles, news and events direct to your inbox
Read more articles tagged: Cyber Security, Featured